CTIN has discovered a new campaign that appears to be associated with previous malicious infrastructure attributed to Evilnum. EvilNum is an advanced persistent threat (APT) group that is characterized by an evolving toolkit and sector-specific and geographic-specific targeting. ESET performed an in-depth technical analysis on observations they made between 2018 and 2020. [1] More recently CyberReason has described one of their newest tools called PyVil Remote Access Trojan (RAT).[2] This is a RAT written in the popular Python programming language. And, as the reader will see in my subsequent analysis, this new campaign appears to be using a compiled version of Python modules (with the .pyd extension). Based on the targeting patterns and the technical analyses from previous researchers we hypothesize that the artifacts we have surfaced provide evidence of a new and currently active EvilNum campaign.
Based on the current evidence EvilNum is focusing on specific targets in the financial services sector in EU countries and the UK. They are particularly interested in banking and financial technology companies and are taking advantage of Know Your Customers (KYC) rules that require these companies to collect personally identifying information (PII) from their customers.
Targeting
In their past campaigns high value targets like customer service representatives and KYC screeners at leading banks and financial institutions are targeted through carefully crafted phishing emails that include a link to a downloadable file. This file appears as a bundle of shortcuts that, when opened, secretly run harmful software in the background while also showing a fake document to distract the user. To further deceive the user, shortcut files are named in a way that makes them look like harmless documents or images. This trick is especially effective on Windows computers, where the type of file is usually not shown, making it easier for the user to be fooled into opening it.
In the current campaign we have not been able to corroborate this method of social engineering. However, through our hunting using network artifacts on threats to upcoming EU-related elections we identified some cyber observables that led us to artifacts that have been associated with past EvilNum campaigns. What we uncovered was an IPv4 and an IPv6 address that resolved to a RU domain name that embedded the word ‘android’. The IPs of interest are:
- 172.67.183[.]146
- 2606:4700:3033::ac43[:]b792
The use of the word ‘android’ led us to surmise that the phishing campaign was 1) targeting android users, or 2) launched from android devices through an extensive affiliate network.
The IPs in question that led us to the domain of interest are registered to Cloudflare. Most reputable US and European companies, like Cloudflare, work closely with law enforcement once malicious activity has been discovered on their infrastructure. In fact, just this week the world witnessed a major global takedown of one of the most egregious botnets by international law enforcement cooperation (along with private sector companies who were owner/operators of the underlying infrastructure).[3] We hope that this report will also interest Cloudflare security researchers which will result in remedial action.
Following is a summary of some of the hunt artifacts that led us to hypothesize that this is a new EvilNum campaign.
SkaCHAT Campaign
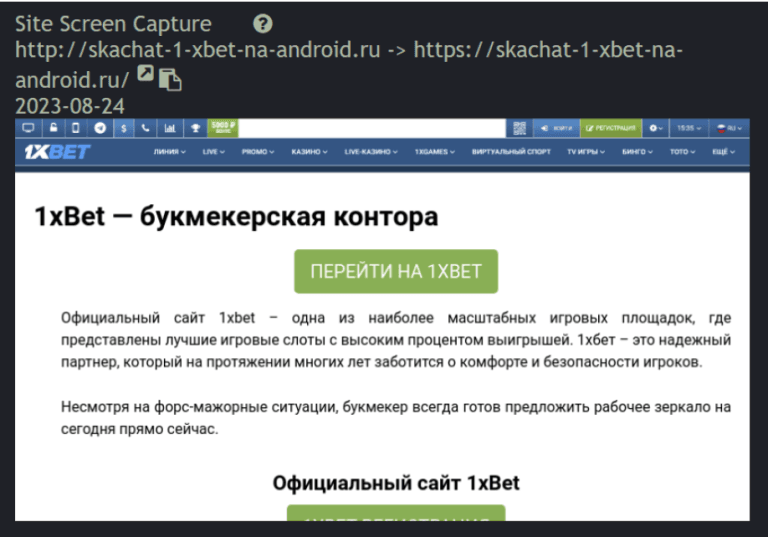
From the 172.67.183[.]146 IP we further investigated the suspicious-looking Russian TLD domain name: skachat-1-xbet-na-android[.]ru. Note that the subject domain was last seen on current DNS servers Sept. 2, 2023. A screenshot of the landing page of the website is given here.
Upon further investigation of the functioning of this site we found evidence of a widespread phishing campaign associated with our subject cyber observables that appeared to be administered from https:// mail.sandiegofenceinstallers.com. Redirect strings were embedded in phishing lures that exposed vulnerable hosts to infection.
Each redirect string embedded the name or names of financial institutions as shown on the example image below.
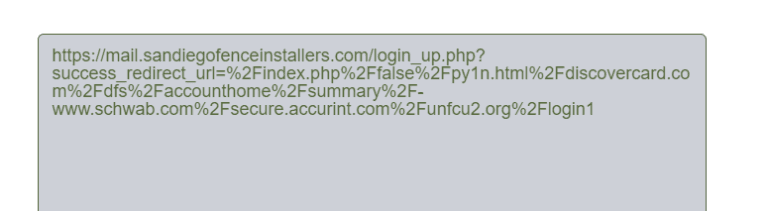
The URL string in the figure above was embedded in a benign chrome executable bundle for a Chrome update. A Joe Sandbox analysis of the redirect string is provided at the following URL: https://www.joesandbox.com/analysis/1296925.
The following flow diagram is a screenshot of the behavioral analysis. As the reader will note from the flow diagram the heat bar for the Google files and IP addresses are benign, whereas the rating for the string we submitted for analysis is flagged as Malicious.
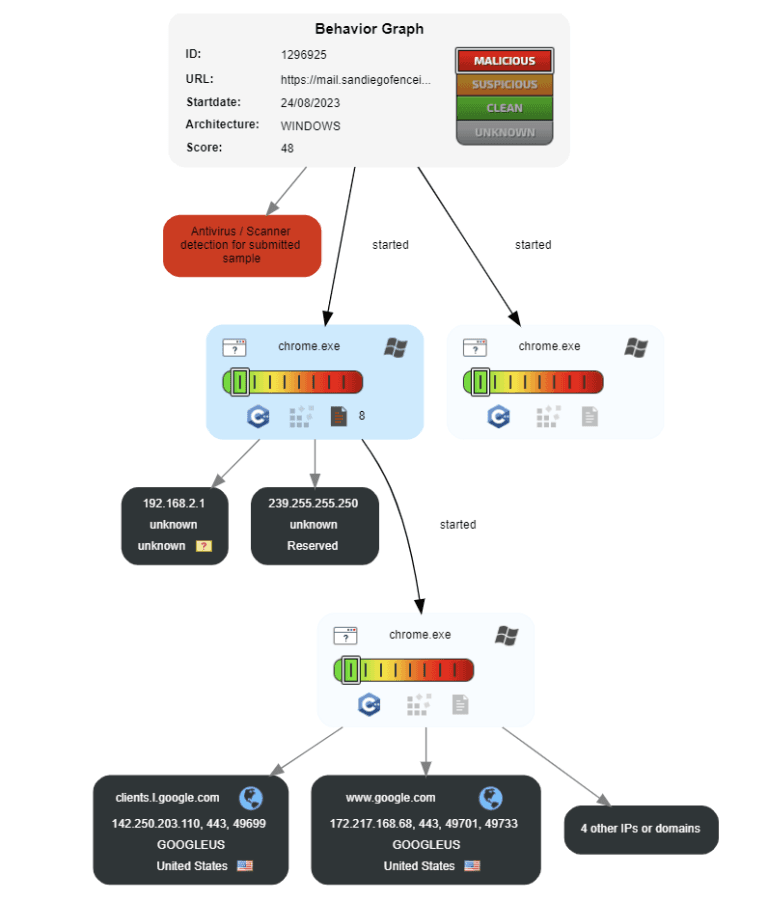
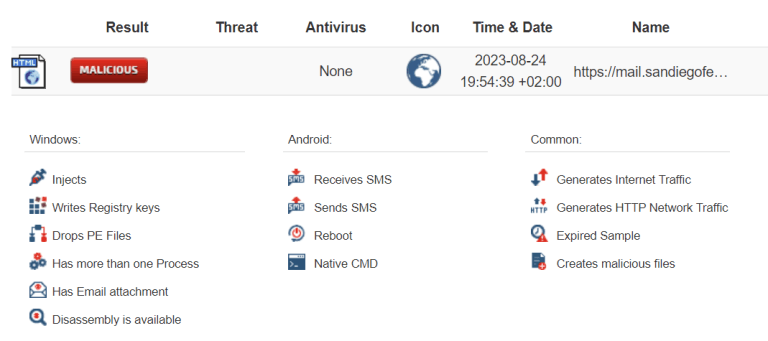
The JoeSandbox analysis run was performed on August 24 at 19:54:39 +02:00 UTC. A summary of the impact on Windows systems includes:
- injects,
- writes to registry keys,
- drops of process executable files,
- multi-threaded processing,
- email attachment and disassembly.
There were also numerous Android and Common behaviors that were identified by the analysis as summarized on the above figure.
A VirusTotal hunt on that MD5 hash takes us to a Chrome executable file that shows up Clean as of August 29, 2023 23:35:36 UTC (https://www.virustotal.com/gui/file/435ef71c00333bddecf5b30c491327b573461051baa9d6b71063d79783589fa9/detection). This is as we would expect, given the results of the JoeSandbox analysis.
However, there were Community Collections showing relationships with an underlying malicious infrastructure. We explored some of the findings of these Community Collections and surfaced more artifacts using the Graph analysis capabilities of VirusTotal.
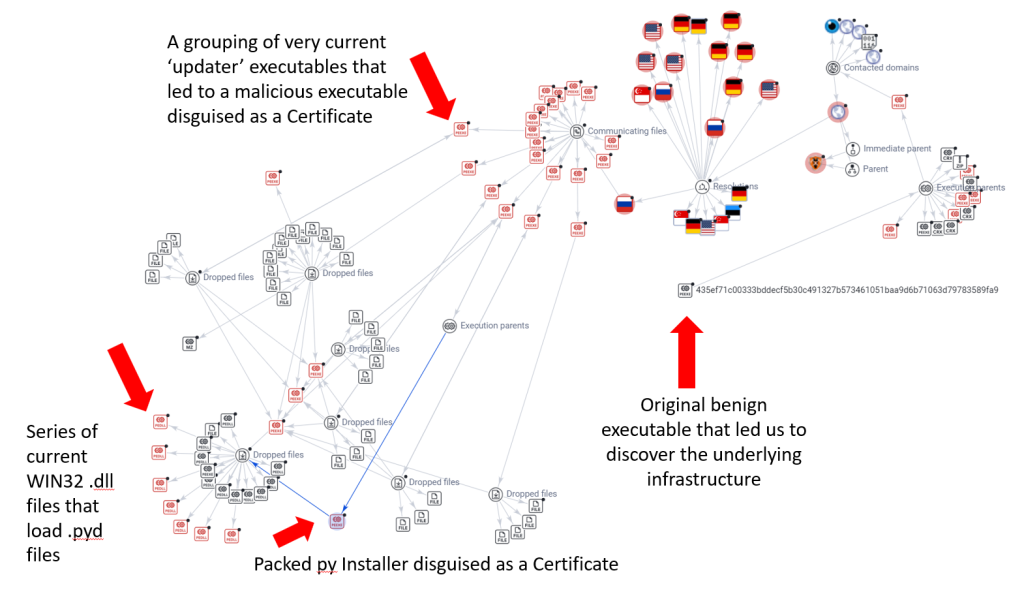
On the bottom right of the figure is a cluster of very current .dll files that are designed to perform actions that load or execute .pyd files as part of an attack chain. A .dll file cannot “contain” a .pyd file in the sense of embedding it within its binary structure, as both are standalone compiled binaries.
The .pyd file extension represents a Python Dynamic Module. These are analogous to dynamic link libraries (DLLs) on Windows or shared objects (.so) on Linux and Unix systems. A .pyd file is basically a DLL but is loaded like a regular Python module. It can contain compiled C or C++ code and is generally used to extend the capabilities of Python by allowing the integration of functions written in languages like C and C++.
When you import a .pyd file in Python, the Python interpreter treats it just like a regular Python module, but the actual code execution happens in the compiled code contained within the .pyd file. This approach is often used for performance optimization or for integrating Python with libraries written in other programming languages.
In a cybersecurity context, .pyd files could potentially be scrutinized during threat hunting activities. Since they can contain compiled code, they have the capacity to perform actions that could be malicious, similar to other forms of compiled code like DLLs or executables.
However, a .dll file can be designed to interact with a .pyd file, and vice versa, if they are programmed to do so. For example, a Python program using ctypes or pybind11 could load both .dll and .pyd files and facilitate interaction between them, allowing for a kind of functional relationship even if one does not contain the other.
As can be seen on the above figure, the .dll files that load the .pyd files have been packed by a py Installer file called CertReq[.]exe, last seen Aug. 2, 2023, visible at the bottom left.
The above graph image can be accessed live at:
At this juncture it should be noted that the ‘sandiegofenceinstallers[.]com’ domain that was embedded in the phishing campaign was what led us to these artifacts. This domain currently presents as ‘clean’ on VirusTotal (as of August 29, 2023). The WHOIS information indicates that it is owned by Alibaba as of April 10, 2023, as shown on the adjacent figure. The embedded redirect string we discussed above is not being picked up by traditional antivirus signature-based solutions.

Sample domains embedded in the strings are given below:
- accountmanagepymnt.myvnc.com
- summarypaymentsacc.myftp.org
- manageaccountpaymnt.myftp.org
- info6547makingreal.ddns.net
- paypalsemewq.servebeer.com
- limitedppmanageaccountous.forumz.info
The specific activity associated with the malware discovered in this has not been confirmed as the PyVil RAT as analyzed by CyberReason. However, the evidence discovered suggests that the current campaign may be an extension of previous activity targeting financial services with some of EvilNum’s newest tools.
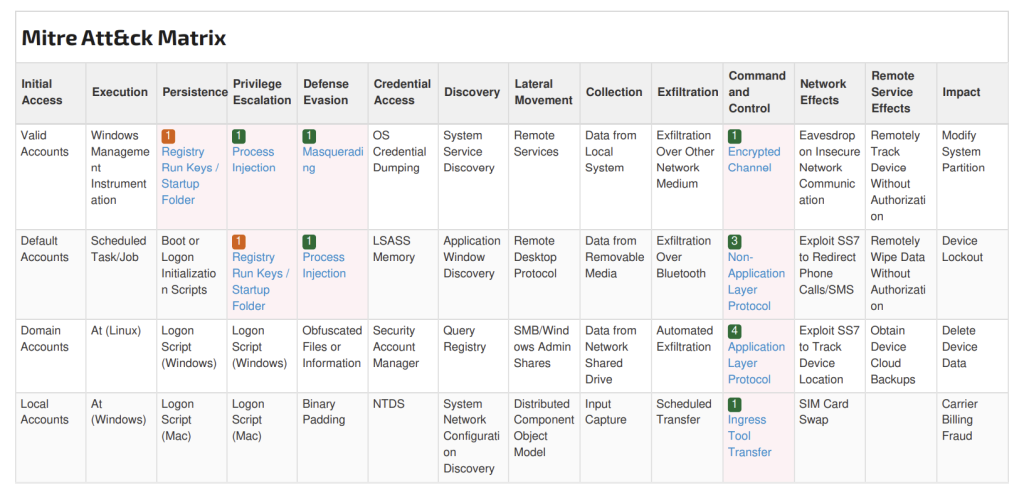
When applying our findings regarding the ‘sandiegofenceinstallers[.]com’ domain to the MITRE ATT&CK Matrix, the specific tactics, techniques and procedures (TTPs) of the malicious redirect code and subsequent infection chains can be surfaced.
The specific TTPs are given in the figure below.
Conclusions
Evilnum is a recognized threat actor group that has been active since 2018. Multiple technical analyses have been published outlining their advanced TTPs and targeting patterns. This article adds to that knowledge base by revealing the finding of our research in late summer, early fall of 2023, a pivotal time in the geopolitical context.
Based on our evidence to date our test of the alternative hypotheses about the use of, or targeting of, android hosts would lead us to conclude that the latter was the case. This is based on the findings from the JoeSandbox analysis that illustrated specific functions that were surfaced during the behaviorial analysis.
We were also able to surface a domain that appeared to be a key domain for distribution of strings spreading the phishing campaign (sandiegofenceinstallers[.]com). We are characterizing this as a C2 Phishing domain. We also saw that this domain was injected onto legitimate updates of the Chrome web browser.
Furthermore, we have documented the files that have been most active in the spread of a Python module. All of the modules identified have been active since July, 2023. We cannot corroborate the use of the PyVil RAT as described by CyberReason, but we can assert that the threat actor appears to be using a Python-based infrastructure.
Indicators of Compromise (IOCs)
IP Addresses:
- 172.67.183[.]146
- 2606:4700:3033::ac43[:]b792
C2 Phishing Domain:
sandiegofenceinstallers[.]com
.pyd Installer File:
CertReq[.]exe
Indicators of Compromise (IOCs)
IP Addresses:
- 172.67.183[.]146
- 2606:4700:3033::ac43[:]b792
C2 Phishing Domain:
sandiegofenceinstallers[.]com
.pyd Installer File:
CertReq[.]exe
Editors Note: The Sigma Signature below was published as OSINT to the VirusTotal platform. Credit goes to the author: Ariel Millahuel. The MITRE ATT&CK TTPs cited here are for the PyVil RAT, not for the sandiegofenceinstallers[.]com domain as shown above.
Sigma Rule – Pyvil RAT
action: global
title: Pyvil RAT
status: stable
description: Pyvil its a new RAT that belongs to the Evilnum group. This one was highly investigated by the Cybereason’s Nocturnus Team. Also, its important to say tha this is a python-scripted RAT.
references:
– https://tdm.socprime.com/tdm/info/YgyDYAROBUOq
– https://www.cybereason.com/blog/no-rest-for-the-wicked-evilnum-unleashes-pyvil-rat
– https://attack.mitre.org/techniques/T1566/002/
– https://attack.mitre.org/techniques/T1566
– https://attack.mitre.org/techniques/T1059/003/
– https://attack.mitre.org/techniques/T1059
– https://attack.mitre.org/techniques/T1027/
tags:
– attack.defense_evasion
– attack.execution
– attack.t1566
– attack.t1059
– attack.t1059.003
– attack.t1027
author: Ariel Millahuel
detection:
condition: 1 of them
fields:
– EventID
– CommandLine
– TargetFilename
falsepositives:
– none
level: critical
—
logsource:
product: windows
service: sysmon
detection:
selection1:
EventID: 11
TargetFilename|contains:
– PersonalKYC.pdf.lnk
– 1.lnk
– \Microsoft\Credentials\MediaPlayer\ddpp.exe
– \microsoft\media player\player\fplayer.exe
—
logsource:
category: process_creation
product: windows
detection:
selection2:
CommandLine:
– cmd.exe /c path=%windir%\system32&move “PersonalKYC.pdf.lnk” “%tmp%\1.lnk”&type “%tmp\1.lnk” |find “END2”>”%tmp%\0.js”&wscript “%tmp%\0.js”Mul
Editors Note: The Sigma Signature below was published as OSINT to the VirusTotal platform. Credit goes to the author: Ariel Millahuel. The MITRE ATT&CK TTPs cited here are for the PyVil RAT, not for the sandiegofenceinstallers[.]com domain as shown above.
Sigma Rule – Pyvil RAT
action: global
title: Pyvil RAT
status: stable
description: Pyvil its a new RAT that belongs to the Evilnum group. This one was highly investigated by the Cybereason’s Nocturnus Team. Also, its important to say tha this is a python-scripted RAT.
references:
– https://tdm.socprime.com/tdm/info/YgyDYAROBUOq
– https://www.cybereason.com/blog/no-rest-for-the-wicked-evilnum-unleashes-pyvil-rat
– https://attack.mitre.org/techniques/T1566/002/
– https://attack.mitre.org/techniques/T1566
– https://attack.mitre.org/techniques/T1059/003/
– https://attack.mitre.org/techniques/T1059
– https://attack.mitre.org/techniques/T1027/
tags:
– attack.defense_evasion
– attack.execution
– attack.t1566
– attack.t1059
– attack.t1059.003
– attack.t1027
author: Ariel Millahuel
detection:
condition: 1 of them
fields:
– EventID
– CommandLine
– TargetFilename
falsepositives:
– none
level: critical
—
logsource:
product: windows
service: sysmon
detection:
selection1:
EventID: 11
TargetFilename|contains:
– PersonalKYC.pdf.lnk
– 1.lnk
– \Microsoft\Credentials\MediaPlayer\ddpp.exe
– \microsoft\media player\player\fplayer.exe
—
logsource:
category: process_creation
product: windows
detection:
selection2:
CommandLine:
– cmd.exe /c path=%windir%\system32&move “PersonalKYC.pdf.lnk” “%tmp%\1.lnk”&type “%tmp\1.lnk” |find “END2”>”%tmp%\0.js”&wscript “%tmp%\0.js”Mul