by Ben Tomhave
In preparation for an upcoming talk, I ended up going down the path of reading up on the recent history of technological advances, highlights of malware and attack evolution, the highlights of infosec innovation, and landmark laws and regulations that have impacted infosec and privacy. Yes, that’s a mouthful, but it turned out to be very interesting. And, since I bugged people online and on lists to help with input, I figured the least I could do was to summarize my findings as best as possible here.
Overall Impressions
Reviewing the history of the last 100 years (less, really) with an eye on infosec and privacy was an intriguing process. Maybe some day I’ll be able to spend more time on it. As you’ll hopefully see below, I think that my research reinforces a couple notions.
We’re still in a transitional period in time. The Industrial Revolution lasted 100 years (1750-1850), and was followed by what’s termed the “Second Industrial Revolution,” which itself lasted another 70 years, give or take. For comparison, this timeframe precedes American independence (1776), runs through the American Civil War (1861-1865), and on until World War II (1939-1945). That’s a phenomenally long timeframe.
Now, clearly, that nearly 2 centuries of time can be partitioned into sub-eras, and rightly so, but my point is this: it takes a generation to adapt and adopt to new technologies. As I note in the referenced piece, there are myriad examples in vehicle safety and industrial safety that show just how long it takes humans to account for and manage new risk factors that result from adoption of technological advancement.
As such, my belief is that we will eventually exit this transitional period and achieve a new equilibrium. However, reaching such a point is probably 25-50 years away (maybe even longer out). And, unfortunately, until humans evolve to better inherently manage these new digital risks, the more problems we’re going to continue to experience. One need only look at BYOD and how companies are officially blessing data exfiltration to see a ready example of how our inability to manage human risks can, will, and is coming back to bite us.
So, without further adieu (or rambling)… on to the research highlights…
The Good: Technological Advances
For a starting point, I was curious about when key advances in online transactions occurred. The following graphic shows a quick summary of some key highlights in online computing history. Please note that each of the four graphics presented in this post can be clicked upon to see the original full-size image.
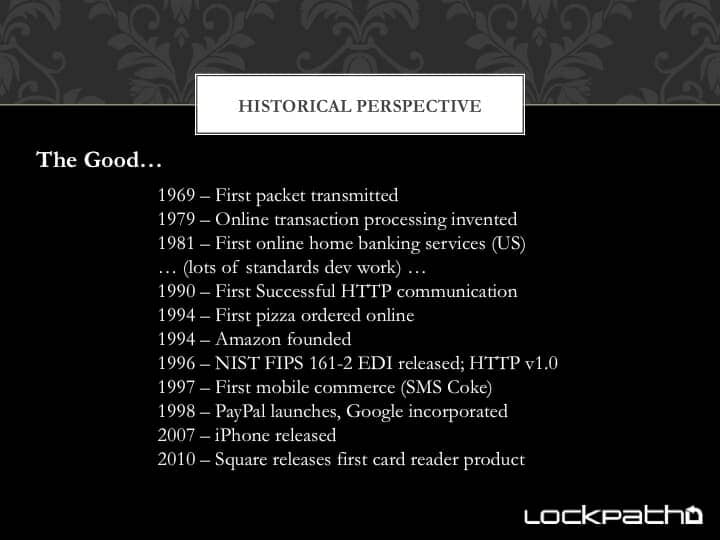 There are a few things worth noting here. First, online banking has actually been around for a loooooong time. Interestingly enough, those early advances and their associated standards eventually evolved into EDI (Electronic Data Interchange, 1996), which itself evolved in parallel to the beginning years of the Internet (dot-com bubble) boom and modern eCommerce.
There are a few things worth noting here. First, online banking has actually been around for a loooooong time. Interestingly enough, those early advances and their associated standards eventually evolved into EDI (Electronic Data Interchange, 1996), which itself evolved in parallel to the beginning years of the Internet (dot-com bubble) boom and modern eCommerce.
Second, there’s a notable gap here in the timeline… and this was done intentionally… for example, AJAX and the whole “Web 2.0” movement definitely falls within that ’98-’07 timeframe, as does the end of the Internet boom (dot-com bust), and many other activities. However, in researching “major advancements” relative to the Internet, I simply could not find anything overly compelling (though I’m sure readers here will chime in if I’ve made any egregious omissions).
Finally, I just want to point out that the iPhone is highlighted as a major turning point (because it was). Note that it’s just been 5.5 years since it came out. That’s not very long! Now, obviously, mobile computing has a much longer history (Wikipedia does a good job capturing the high points), but to me the true turning point, which tabs into the rise of cloud computing (also not noted on the timeline because, frankly, how do you set the “beginning” date for it?) and BYOD, is the iPhone because of it’s “cool” factor, it’s immediate widespread adoption, and because of its impact on other mobile computing platforms.
Much more could be said in this timeline, but I think I’ve captured some of the key dates in order to tell the story that technology has evolved – and continues to evolve – very rapidly. As such, it’s still very difficult for humans to adapt and adjust to the associated risk factors. There can be no equilibrium without a slowing in technological evolution.
The Bad: Malware and Attack Advances
After going down the path of “What kind of cool advancements have occurred?” my next natural question was “How have the bad guys kept pace?” Of course, as anybody in the industry will point out, the attackers have done more than keep pace. In many ways, they’ve pushed the envelope, oftentimes evolving attacks far faster than defenses can be engineered (a point that will stand in bleaker contrast in the next section).
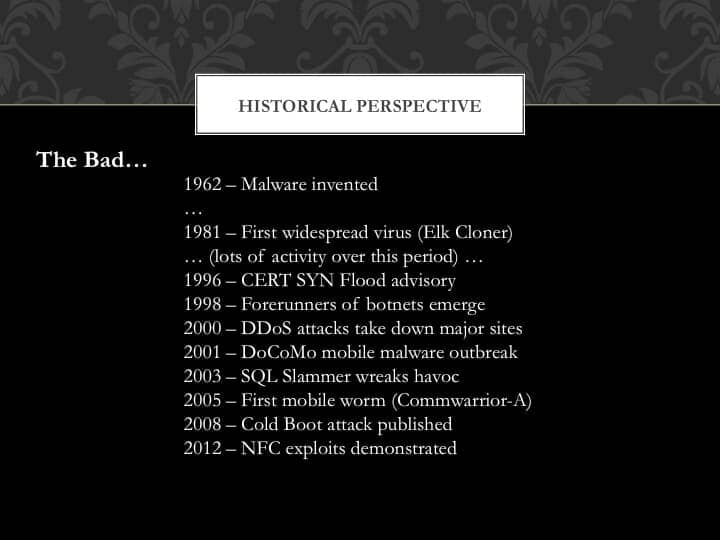 I’ve left out a LOT of smaller landmarks in this summary slide, such as “Rabbit” (1974) and the “Morris worm” (1988). Ultimately, when it came down to narrowing the list, I found that the nuances in malware attacks weren’t nearly as interesting (in the big picture) as some of the larger turning points. Malware that automatically spread in different ways was definitely interesting, such as moving from requiring direct contact with an infected device (a la boot sector viruses) to worms and trojans that auto-propagate across networks and leave backdoors.
I’ve left out a LOT of smaller landmarks in this summary slide, such as “Rabbit” (1974) and the “Morris worm” (1988). Ultimately, when it came down to narrowing the list, I found that the nuances in malware attacks weren’t nearly as interesting (in the big picture) as some of the larger turning points. Malware that automatically spread in different ways was definitely interesting, such as moving from requiring direct contact with an infected device (a la boot sector viruses) to worms and trojans that auto-propagate across networks and leave backdoors.
Overall, attacker history paints a pretty bleak picture. SYN flood attacks date back to the mid-90s. 2000 saw the major DDoS attack that took down the likes of Yahoo! and CNN. The first mobile malware outbreak actually dates back to 2001 in Japan. I well-remember the era of SQL Slammer, Nimda and Code Red in the early 2000s. And so on.
What’s interesting to me, however, is how this contrasts with technological evolution. Consider, for example, that the first mobile worm came out in 2005 – 2 years before the iPhone was released! Also, notice the reference to NFC exploits and attacks from this year (2012) and how that also really precedes or coincides with the emerging use cases for Near Field Communication in mobile devices.
It’s really truly amazing to me just how rapidly the “bad guys” innovate their attack methods, taking advantage of the uncertainty and immaturity that surrounds the introduction of new technologies and use cases. If there is one big lesson to learn here, it’s that we are failing (massively) to learn from history when it comes to releasing new advances, and we’re paying a steep price as a result!
The Ugly: Security Innovation (or the lack thereof)
This line of discussion brings us naturally to the next point, which is to look at major security technology advances along those same timelines. Here is where the picture gets a bit bleak. Technology innovation continues to move at a steady clip, and attacker advancements continue to evolve at break-neck speeds… unfortunately, defensive capabilities are well behind the curve and seemingly losing more ground every day. While we’re certainly getting better at playing catch-up, the fact still remains that defensive technologies are inherently reactionary. In this manner, anybody who believes that we can rely just on defensive technologies is not thinking clearly (more on this below).
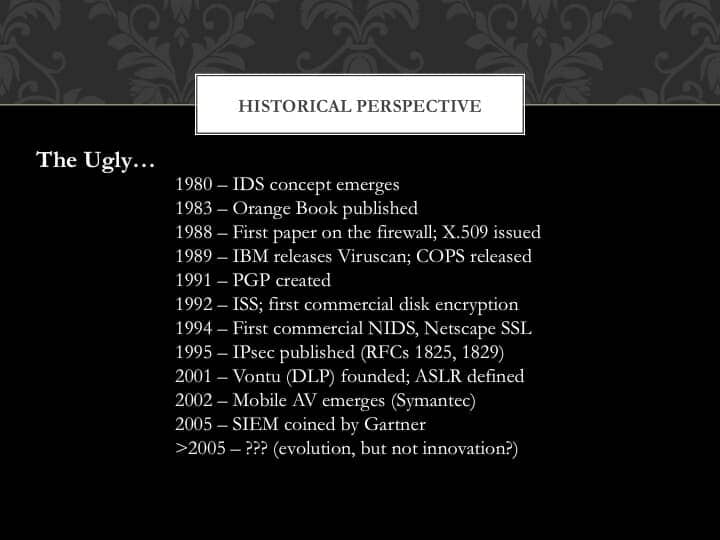 This summary of highlights is perhaps a bit disingenuous as there have certainly been improvements since 2005 (e.g., improvement in and adoption of sandboxing techniques and virtual machines, improved ASLR, improved PRNG (Fortuna), intrusion deception, advanced endpoint protection, signature-less next generation AV, advanced UTMs). However, the point here is that pretty much every one of these advances is an incremental step forward, enhancing an existing concept. In no case could I find any defensive security technologies that truly represented something new. Rather, while the attackers continually innovate and jump the curve along with overall technological advancements, we see that defensive security technologies simply evolve along the same curve, falling ever farther behind.
This summary of highlights is perhaps a bit disingenuous as there have certainly been improvements since 2005 (e.g., improvement in and adoption of sandboxing techniques and virtual machines, improved ASLR, improved PRNG (Fortuna), intrusion deception, advanced endpoint protection, signature-less next generation AV, advanced UTMs). However, the point here is that pretty much every one of these advances is an incremental step forward, enhancing an existing concept. In no case could I find any defensive security technologies that truly represented something new. Rather, while the attackers continually innovate and jump the curve along with overall technological advancements, we see that defensive security technologies simply evolve along the same curve, falling ever farther behind.
One aspect that jumped out at me in doing this research was realizing just how old some concepts and technologies are. Intrusion detection, for example, was first described in the paper “Computer Security Threat Monitoring and Surveillance” written by James P. Anderson in 1980 (meaning that IDS is effectively 32 yrs old!). Similarly, the first paper on firewalls was published by DEC in 1988, which is also the same year that X.509 was initially issued (providing the basis for modern Public Key Infrastructure, or PKI). Another date that jumped out at me was 1994, when Netscape released the first version of SSL. That’s the same year that Amazon, eBay, and Dell were founded, as well as the same year that the first pizza was ordered online (in Silicon Valley, of course!). I find this cross-tabulation of dates and technologies very interesting, though also a bit disappointing given that it’s now been 20-30+ years.
There is another interesting aspect to defensive security technologies, to which I eluded earlier. Pretty much every defensive measure is in response to an attack technique. As such, these technologies are, by their very nature, reactionary and doomed to fix yesterday’s problem. If we’re only ever innovating toward solving the last few classes of attacks, then we’ll never get ahead of the curve. What we need, more than anything else today, is some true innovation that allows us to jump the curve and get back ahead of the game; or, to change the game so completely that entire classes of attacks are ruled out.
More importantly, this means we also cannot rely on prescriptive standards or regulations because they evolve even slower than defensive technologies! I believe that this last point is more widely known and accepted since it does not threaten vendor revenue streams. However, the previous point on the deficiency of the current evolutionary curve in defensive technologies, which lies in lock-step with this final point, does potentially threaten the revenue streams of vendors, and thus seems not to receive adequate consideration. Suffice to say, the opportunity for future success will lie with those able to truly innovate and get out of this evolutionary slog along antiquated lines of thinking. Hopefully programs like DARPA’s Fast Track will help us turn the corner on innovation in defensive security technologies.
The Uglier: Laws and Regulations
Having looked at security innovation, and how prescriptive approaches advocating the use of non-evolved technologies puts us increasingly behind, it is then logical to look at the highlights of legal and regulatory changes in this space. I circulated the below list in draft form (several revisions) to the ABA SciTech InfoSec Committee to garner feedback on my research. This effort was very educational, and has even stimulated enough interest from the committee to warrant a formal working group toward producing more on this topic… but I digress…
The point here is that the changes in infosec and privacy law over the past 75-100 years is most interesting. There have been a lot of efforts along the way, and there certainly is no way to capture everything. Hopefully you’ll find this list to be informative.
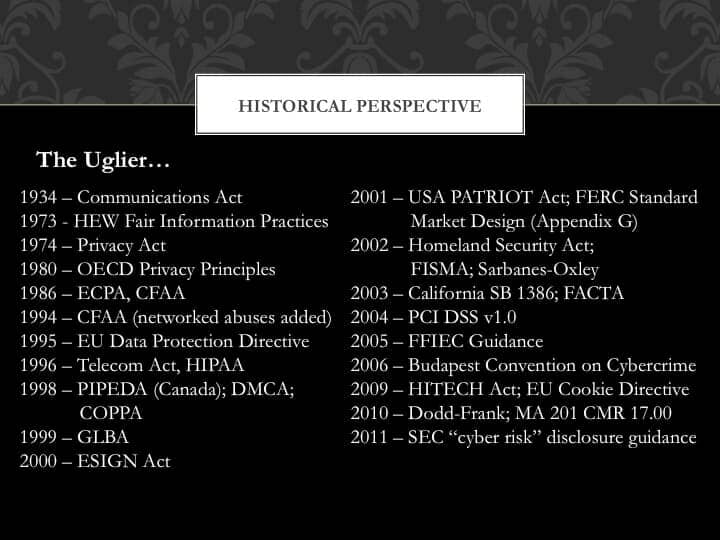 Before going into further analysis, it’s worthwhile to share a few notes on my selection process. In building this list, I sought out those laws and regulations that seemed to be most impactful on the industry. In most cases I tried to avoid State regulations because there are just too many to track. At the same time, there were a couple examples that simply could not be omitted. Similarly, the list does tend to be US-centric, but that is due largely to my being based in the US and not having access to foreign regulations. I’ve included a few non-US acts to provide a more complete picture within the timeframe.
Before going into further analysis, it’s worthwhile to share a few notes on my selection process. In building this list, I sought out those laws and regulations that seemed to be most impactful on the industry. In most cases I tried to avoid State regulations because there are just too many to track. At the same time, there were a couple examples that simply could not be omitted. Similarly, the list does tend to be US-centric, but that is due largely to my being based in the US and not having access to foreign regulations. I’ve included a few non-US acts to provide a more complete picture within the timeframe.
Analyzing this list, the first thing that jumps out at me is this: The left-side list spans 1934-2000 (67 years), while the right-side list spans 2001-2011 (11 years). Both sides have 15 laws or regulations listed. It’s also very evident that the legal and regulatory landscape is changing at an increasingly rapid pace, which makes it incredibly difficult for organizations to stay on top of things. The rate of change in the industry from a legal and regulatory standpoint is astounding, and libel only to get worse.
Note that my list omitted two major releases from this year: EU COM/2012/09 “Safeguarding Privacy in a Connected World A European Data Protection Framework for the 21st Century” and the proposed U.S. Cybersecurity Act of 2012 (which at time of writing hasn’t passed the U.S. Senate, though it’s apparently finding new life again in light of a recent speech by U.S. SecDef Leon Panetta, which received immediate support from U.S. Senate Majority Leader Harry Reid). The EU COM release lays out their planned framework for reworking privacy directives going forward, including a new directive to supplement/replace the ’95 Data Protection Directive and the ’09 Cookie Directive. This likely represents a very strong move forward on privacy rights that will have broad-reaching effects.
A few other notes of interest…
- PCI DSS was released in 2004. It has since gone through a few revisions. Also noteworthy is that three States (WA, MN, and NV) have adopted all or part of it as State law (NV simply requires full compliance).
- CFAA originated in the mid-1980s, but didn’t include coverage of networked abuses until the 1994 update, which is why that year was chosen.
- FERC Standard Market Design (Appendix G) is listed rather than the NERC CIP standards, since the FERC document triggered the entire initiative.
- Note that FACTA is mapped against 2003 even though the “Red Flags” provision wasn’t really implemented until after the Red Flag Program Clarification Act of 2010 was signed into law due to some jurisdictional and enforcement concerns with the original legislation.
- A handful of acts were passed in the late 1990s (e.g, HIPAA, DMCA, COPPA, GLBA), but their effect really wasn’t felt much until after 2000.
- The only two State bills listed – CA SB 1386 and MA 201 CMR 17.00 – were included because they represented leading-edge shifts in policy. The CA bill signified the first real legal requirement for breach disclosure, whereas the MA act mandates that businesses have formal, written, routinely audited plans in place for protecting personal information. The MA law is about the closest thing we’ve seen to a legal mandate for “commercially reasonable” security practices around protecting PII.
- The Budapest Convention (2006) and the DMCA (1998) both represent interesting moments where the U.S. has made changes to how they handle copyright enforcement and protection of intellectual property. These acts are an interesting contrast to the SOPA/PIPA drafts that failed to pass the U.S. Congress in 2012, and their relation to the ACTA treaty. While SOPA and PIPA are deemed “dead” now, it’s probably premature to think that ACTA supporters won’t try to find another way to get it ratified by the U.S., with comparable legal measures in place supporting it.
Obviously much more could be said here, but these highlights hopefully give a glimpse of some key legal and regulatory changes throughout (fairly recent) history.
Closing Thoughts
“Those who cannot remember the past are condemned to repeat it.” (George Santayana)
History can be fascinating to study, delivering many interesting lessons, and providing opportunities to view parallels in development and evolutionary cycles. At the same time, we have to be careful not to see history as a predictor of the future; rather, it is better to learn lessons and then jump to new levels of performance.
Several lessons can be gleaned from the above highlights. Defensive security technologies, while reactive by their very nature, don’t seem to be keeping pace with advances by attackers or even with technological advancements. The legal and regulatory environment is only now starting to come to grips with the digital industrial revolution, and is thus accelerating changes, for better or for worse.
In the end, it’s clear that it will take a generation (or more!) for this digital industrial revolution to achieve a new stasis (or equilibrium) point, and for human evolution to naturally catch up. Until then, we need to double-down on finding new, innovative approaches that allow us to “jump to the next curve” with defensive security technologies. We also need to be careful with advancing legal and regulatory frameworks to make sure that they target the right desired objectives, and to ensure that they do not devolve into prescriptive guidance that will be immediately found to be outdated and inadequate. As a society, we still haven’t had that “ah ha!” moment where humans natively understand how to deal with modern technology risks. Until then we must carry on diligently and hope for a better tomorrow.
Reprinted under the Creative Commons license from The Falcon’s View

